OT/IT Security & Convergence
High-integrity intelligence requires a foundation of absolute data security. We bridge the gap between OT and IT systems to create a unified data environment, protected by a Zero Trust architecture that secures your information at the data level, not just the network level.
Data-Centric Protection
Traditional security focuses on "the castle walls". We focus on the data itself, ensuring that even if a network is breached, your sensitive information remains encrypted and inaccessible to unauthorized actors.
Edge-to-Edge Encryption: Continuous protection that follows your sensitive data wherever it resides across your entire network.
Zero Trust Architecture: Every access request is fully authenticated, authorized, and encrypted before granting access, regardless of where the request originates.
Edge Processing: By utilizing edge-based security, we encrypt data at the point of creation—whether on a mobile device or an IoT sensor—before it ever touches the cloud or a database.
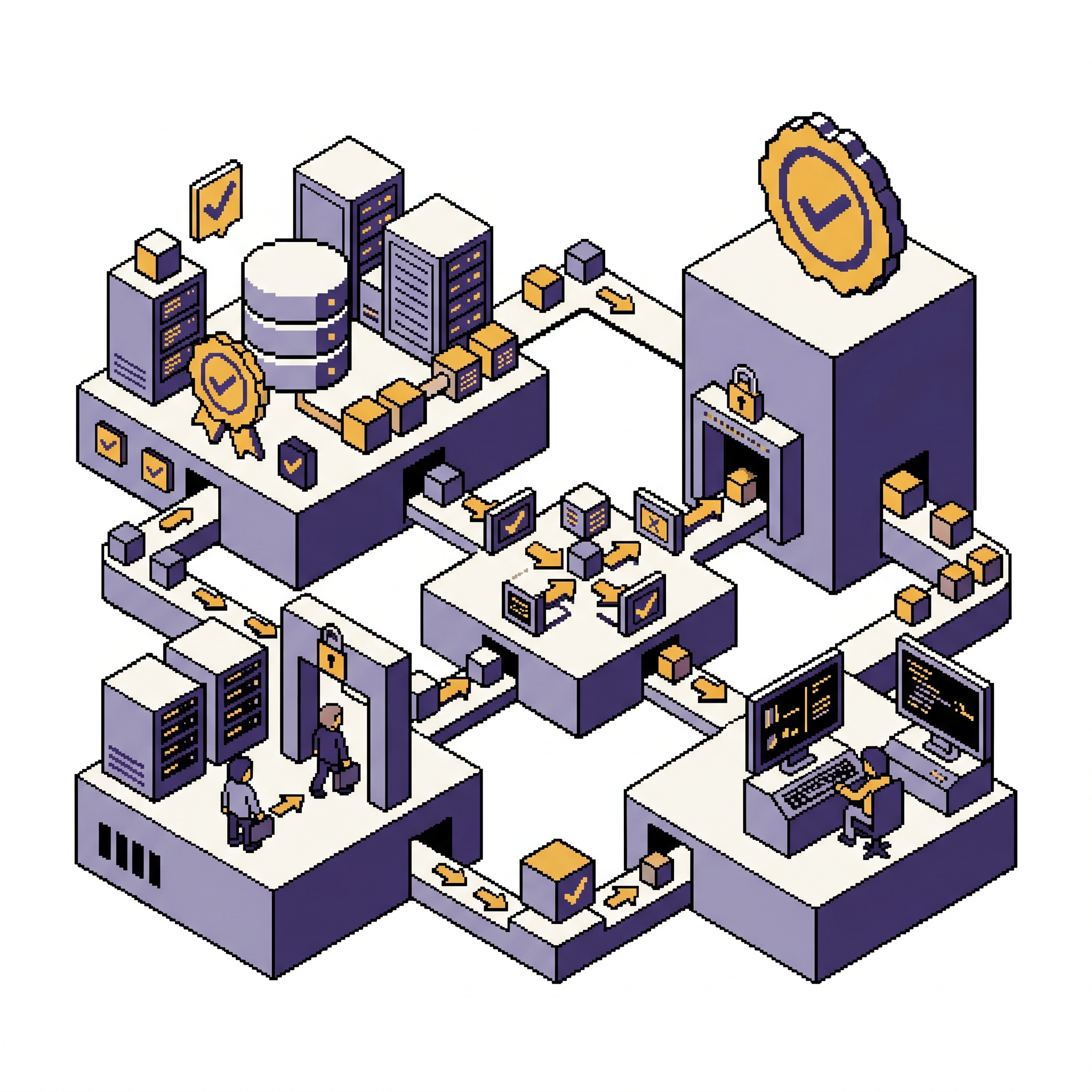
Breaking Down Silos
We unify real-time shop-floor data with enterprise-level analytics to provide a single pane of glass for your operations. This visibility reduces downtime, optimizes supply chains, and enables predictive maintenance.
Strategic Partner: XQ Message
Through our partnership with XQ Message, we provide a quantum-resistant, zero-trust data protection platform that simplifies complex security workflows.
Self-Protecting Data: We engineer solutions where the data protects itself through decentralized key management, ensuring no single point of failure.
Granular Access Control: Real-time visibility and control over who can access your data, for how long, and from what location.
Compliance & Auditability: Every interaction with your data is tracked and audited, meeting the most stringent regulatory requirements for privacy and security.
Capabilities & Solutions
Secure Key Management: Robust encryption management and strict access controls ensuring only authorized users interact with mission-critical information.
Secure Tenant Migrations: Expertly managing the movement of data between cloud environments while maintaining strict security protocols and data integrity.
Transparent Security Logic: We build secure, explainable AI and BI platforms where security isn't a "black box" but a transparent, governed process.
Cyber Resilience: Strengthening your organizational posture against ransomware and data exfiltration through advanced encryption and identity verification.
Bridging the Air-Gap
Translating legacy industrial protocols like Modbus, BACnet, OPC-UA into secure, cloud-ready data streams, ensuring that your mission-critical hardware remains protected while fueling your BI dashboards.
Executive-Ready Security
We bridge the gap between critical industrial infrastructure and leadership clarity. Our converged security solutions are designed to empower executives to make confident, high-velocity decisions, knowing that their operational technology and business intelligence are shielded by the highest levels of integrity.


